Incoming Communication Record Audit – anamedeiro99, Anatarvasa, Asheshshyaam, axxin882, Babaijabeu, Business Ftasiastock, Dfqrbrb, Dhvlwlw, dianaandr3a, Doumneh
The incoming communication record audit presents a method to verify who said what, when, and why, with a focus on accountability and durable access. Voices such as anamedeiro99, Anatarvasa, Asheshshyaam, axxin882, Babaijabeu, Business Ftasiastock, Dfqrbrb, Dhvlwlw, dianaandr3a, and Doumneh contribute annotations as events unfold, preserving context and dissent. The approach remains skeptical about gaps, privacy, and provenance, while insisting on transparency and traceability. What gaps remain unaddressed, and how might future events alter the audit trail?
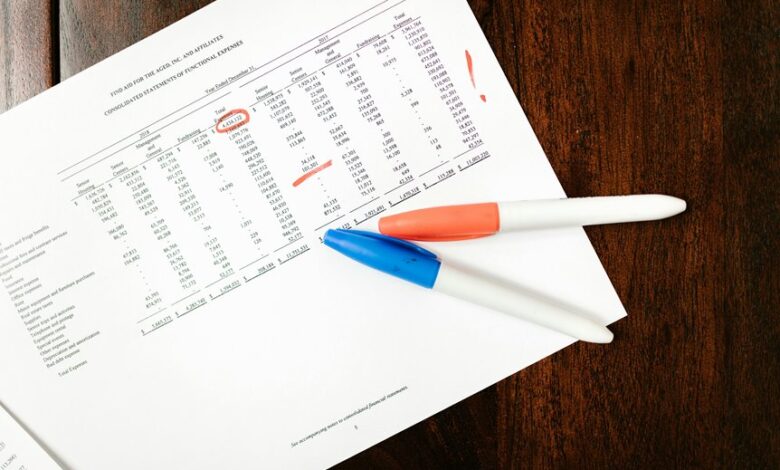
What Is Incoming Communication Record Audit?
An incoming communication record audit is a systematic evaluation of how inbound messages are captured, stored, and retrievable within an organization’s messaging systems. It emphasizes precise governance and consistent methods to preserve integrity. Clear records must be maintained, and audit transparency sustained. The approach remains thorough, skeptical, and precise, targeting freedom through verifiable accountability, reproducible results, and durable data accessibility.
How Voices Shape Audit Trails in Real-World Teams
Voices within teams actively shape audit trails by annotating, contesting, and clarifying the record as events unfold. In real-world settings, incoming communication becomes a living artifact, not a passive log. Stakeholders scrutinize entries, flag ambiguities, and preserve contested moments. This skepticism preserves accountability, ensuring audit trails reflect dissent, resolution, and context, rather than streamlined convenience or erroneous certainty.
Patterns, Risks, and Compliance in Collaborative Messages
Patterns, risks, and compliance in collaborative messages reveal how information flows, is interpreted, and becomes part of the audit record. The analysis remains thorough yet skeptical, examining patterns alignment of messages and their contextual cues. It identifies gaps, ambiguity, and potential misinterpretation, while emphasizing risks mitigation techniques, governance checkpoints, and verifiable provenance to support accountability without compromising the audience’s freedom to inquire.
Best Practices for Transparent, Traceable Communication
Best practices for transparent, traceable communication demand a structured approach that leaves a verifiable record of what was said, by whom, and under what context. The method emphasizes accuracy, auditability, and minimal interpretation, while guarding privacy preservation and exposing ethical considerations. Skeptical evaluation ensures safeguards against manipulation, enabling freedom through accountable discourse and clearly defined retention, access limits, and verifiable provenance.
Conclusion
The incoming communication record audit offers a meticulous, skeptical lens on how each contributor’s input is captured, time-stamped, and preserved for accountability. It reveals patterns and gaps, highlighting where dissent or context may be at risk of drift without rigorous provenance. Is a transparent trace truly inseparable from trust, or merely a curated illusion of reliability? In this framework, every event becomes a verifiable thread, enabling durable inspection while challenging assumptions about seamless collaboration.