Audit Incoming Call Records – 2245096119, 887831407, 83512250804, 3372695110, 8332990168, 3509104130, 2536500841, 2673979949, 7052297336, 6313930636
The audit of incoming call records identifiers 2245096119, 887831407, 83512250804, 3372695110, 8332990168, 3509104130, 2536500841, 2673979949, 7052297336, and 6313930636 demands a disciplined provenance review. Questions of completeness, traceability across telephony, CRM, and auth systems, and precise timestamping must be pressed. Signals must be cross-verified for caller authenticity, while anomalies and attribution gaps are mapped to data lineage. The implications for governance and accountability warrant careful consideration as gaps may emerge.
What Auditing Incoming Call Records Solves
Auditing incoming call records serves to verify the integrity and completeness of call data, ensuring that every interaction is accurately captured and traceable. The practice clarifies audit governance structures and reinforces accountability. It also illuminates data lineage, revealing how records originate, transform, and persist. Skepticism ensures gaps are exposed, fostering freedom through verifiable, transparent archival standards.
How to Validate Caller Authenticity Across Systems
To validate caller authenticity across systems, organizations should implement a structured, cross-platform verification workflow that correlates identity signals from telephony, customer databases, and authentication services.
The approach emphasizes meticulous data provenance and rigorous data lineage tracking, ensuring each signal is traceable and timestamped. Skepticism guards against stitching errors; clarity supports freedom to audit, verify, and challenge questionable provenance without bias.
Detecting Anomalies and Attribution Gaps in Call Data
Anomalies in call data and attribution gaps arise when signal streams fail to align across sources, undermine confidence in provenance, or exhibit inconsistent timestamps. Systematic anomaly detection scrutinizes cross-source congruence, metadata integrity, and sequencing. Analysts quantify deviations, flag anomalous patterns, and map attribution gaps to data lineage, ensuring transparent provenance while preserving analytical freedom and resisting complacent acceptance of noisy signals.
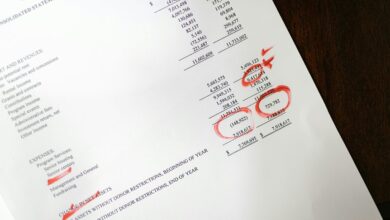
Practical Toolkit and Workflows for Scalable Audits
How can a scalable approach to audits be implemented without sacrificing rigor? A practical toolkit emphasizes modular workflows, repeatable checks, and auditable logs. It prioritizes data provenance, automated validation, and risk-based sampling. Call data integrity and Authentication channels are central, ensuring traceability and secure access. Skepticism drives continuous refinement, avoiding overreach while embracing disciplined scalability for freedom-oriented organizations.
Conclusion
Conclusion: A rigorous provenance-driven audit of these call records must be methodical, skeptical, and traceable from telephony, CRM, to auth systems. Each record should undergo completeness checks, timestamp and lineage cross-checks, and cross-platform caller signals validation. Anomalies and attribution gaps must be mapped to data lineage, with risk-based sampling and auditable logs. As the adage goes, “trust, but verify”—and verify again, until signals align, gaps close, and accountability is assured.