Account & Network Integrity Inspection – mumflexsai4, nbllas95233wm, Nhbgvfqlhbv, Nishidhasagamam, Njgcrby
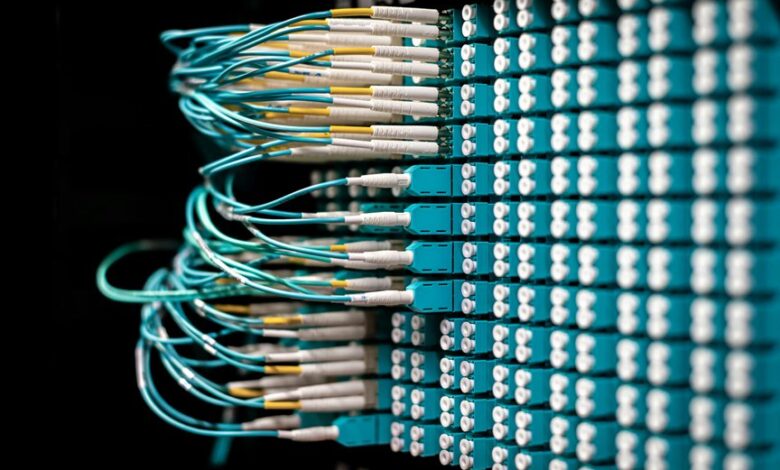
Account and Network Integrity Inspection presents a layered, data-driven framework aimed at real-time detection and remediation of violations. The approach emphasizes anomaly detection in access patterns, credential use, and governance-backed decisions, while preserving user autonomy and privacy. Metrics are defined, preserved evidence is prioritized, and role-based controls guide actions. The method remains methodical and skeptical of false positives, ensuring accountability without overreach. The discussion then turns to practical implementation, inviting scrutiny of its safeguards and tradeoffs.
Account and Network Integrity: How It Works in Practice
Account and Network Integrity operates through a layered set of controls designed to detect, deter, and remediate violations in real time. The approach emphasizes anomaly detection, scrutinizing access patterns to identify unusual behavior. Risk mitigation is proactive, balancing security with privacy considerations. The method remains skeptical, empirical, and transparent, ensuring defenses function without overreach, while preserving user autonomy and freedom.
Detecting Anomalies: From Credentials to Access Patterns
Detecting anomalies in authentication and access stages requires a disciplined, data-driven approach that traces credential usage to behavior across the network.
The analysis emphasizes anomaly detection within access patterns, evaluating credential hygiene and route consistency.
Methodical scrutiny reveals deviations, guiding resilience improvements.
Skeptical examination anchors conclusions in reproducible evidence, ensuring security controls align with organizational freedom to operate without undue constraint.
Measurement, Monitoring, and Metrics That Matter
The approach is thorough yet skeptical, emphasizing disciplined data collection, clear baselines, and disciplined governance.
Metrics prioritize disaster recovery readiness and data minimization, avoiding excessive logging.
Findings enable auditable decisions, revealing gaps without sensationalism, preserving freedom through transparent, purpose-driven instrumentation and accountable stewardship.
Proactive Risk Mitigation: Response Playbooks and Privacy Considerations
Proactive risk mitigation relies on structured response playbooks and privacy-conscious practices that are repeatable, auditable, and adaptable to evolving threats. The analysis remains methodical rather than reactionary, examining role based controls and threat modeling as core instruments. Playbooks prioritize isolation, communication, and evidence preservation while safeguarding privacy. Skeptical scrutiny ensures compliance, transparency, and freedom from overreach, avoiding vague promises or unchecked automation.
Conclusion
In closing, the system stands like a patient lighthouse, its beams sweeping credential seas and access currents with methodical skepticism. Each alert is a measured ripple, each policy a reef chart drawn with caution. Anomalies are weighed against governance, privacy, and evidence trails, never rushed to judgment. The architecture persists as a disciplined guardian: transparent, auditable, and ever-vigilant. Yet vigilance remains provisional, always subject to new data, revised playbooks, and the quiet recalibration of risk.