Account Activity Documentation About Cmsteele005 and Monitoring Records
Monitoring account activity for Cmsteele005 is essential for maintaining security. By documenting records systematically, potential issues can be identified early. This approach not only aids in recognizing unauthorized access but also supports the detection of fraudulent transactions. Various tools and methods exist for effective documentation. However, understanding how to identify irregularities remains a critical component in safeguarding sensitive information. The implications of these practices warrant further exploration.
Importance of Monitoring Account Activity
Why is it essential for individuals and organizations to diligently monitor account activity?
Regular scrutiny of account activity is crucial for enhancing account security and understanding user behavior.
By identifying irregular patterns or unauthorized access, they can proactively address potential threats.
This vigilance not only safeguards sensitive information but also empowers individuals and organizations to maintain autonomy over their digital environments.
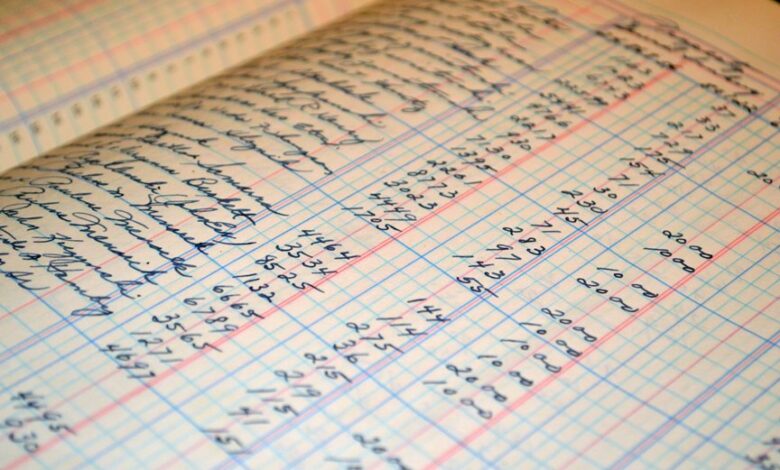
Tools and Methods for Documenting Records
Monitoring account activity is only part of the security equation; the documentation of records plays a vital role in understanding and analyzing that activity.
Effective record keeping strategies involve structured digital documentation, allowing for efficient retrieval and assessment of information.
Utilizing advanced software tools enhances accuracy and reliability, ensuring that all documented records support informed decision-making and promote a secure online environment.
Identifying Irregularities in Account Activity
How can irregularities in account activity be effectively identified?
By monitoring for suspicious transactions and analyzing account anomalies, one can detect potential fraud or misuse.
Regular audits and automated systems can highlight unusual patterns, such as unexpected withdrawals or transfers.
A keen eye for detail in transaction history is essential, ensuring that freedom in financial activities is safeguarded against potential threats.
Best Practices for Safeguarding Sensitive Information
Although sensitive information is crucial for operational integrity, protecting it from unauthorized access and potential breaches is paramount.
Implementing robust access controls ensures that only authorized personnel can access sensitive data. Additionally, employing data encryption safeguards information during transmission and storage, minimizing the risk of exposure.
These best practices are essential for maintaining confidentiality and promoting trust in organizational processes.
Conclusion
In conclusion, the diligent monitoring and documentation of account activity for Cmsteele005 are paramount in safeguarding sensitive information. By employing modern tools and systematic methods, users can effectively identify irregularities akin to a vigilant lighthouse guiding ships through treacherous waters. Adhering to best practices ensures that the integrity of the account remains intact, fostering trust and security in an ever-evolving digital landscape. Regular audits will serve as the compass, directing efforts toward enhanced protection against potential threats.




